Enabling Multi-Factor Authentication in Azure
February 28, 2016 Leave a comment
Azure Multi-factor authentication is a method of validating who you are, which involves the use of more than one verification methods. It provides an additional layer of security to user authentication and transactions.
Azure Multi-Factor Authentication helps to safeguard access to data and applications. It delivers strong authentication with a range of easy verification options such as phone call, text message, or mobile app notification. It also allows users to choose the method they prefer.
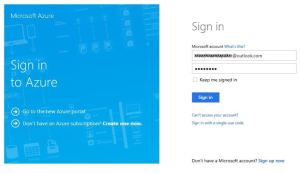
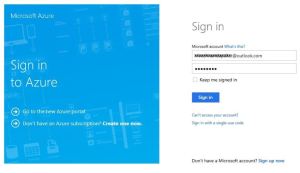
To Enable Multi-Factor Authentication, logon to the Azure management portal (http://manage.windowsazure.com)
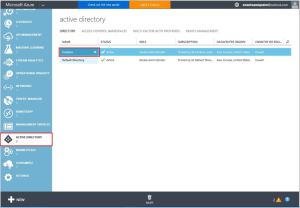
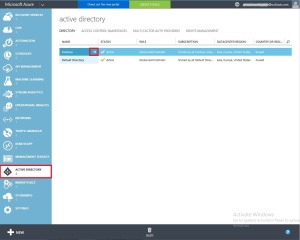
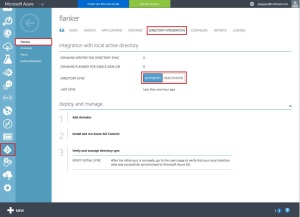
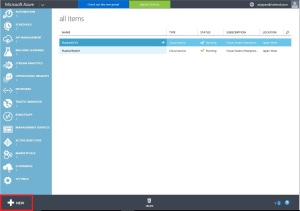
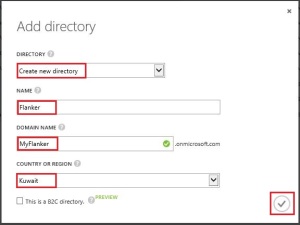
Click on Active Directory and select your Directory Services.
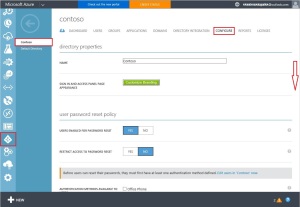
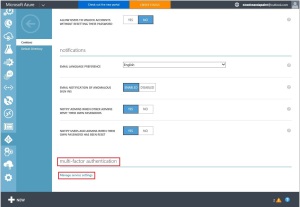
Navigate to the Configure tab of your directory and scroll down until you see the multi-factor authentication section
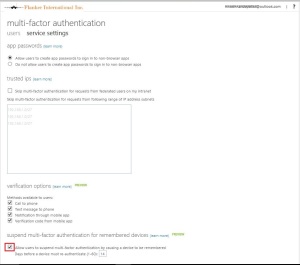
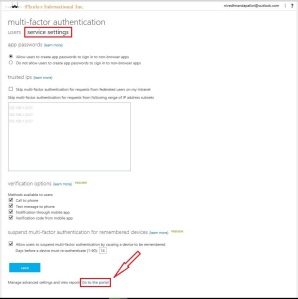
Click on the manage service settings link. This will open the multi-factor authentication administration portal.
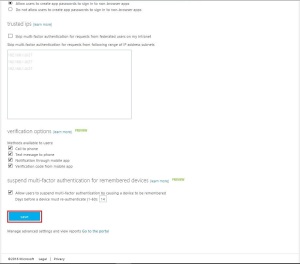
At the bottom of the first page, select the checkbox Allow users to suspend Multi-Factor Authentication by remembering their devices and keep the default set to 14 days.
This will allow the user to remember a device when using MFA. Which means the second factor of authentication is not prompted for unless they come from an unknown device.
Keep everything else set to defaults.
Click the Save button to commit your changes.
Once the operation completes, click the Close button to go back to the MFA administrative portal.
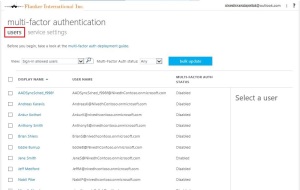
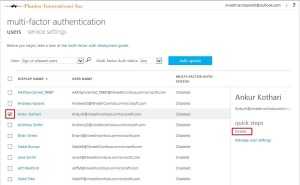
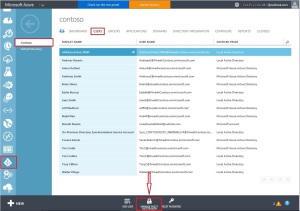
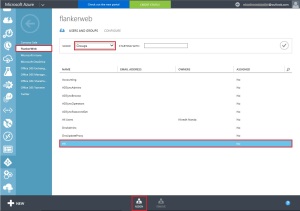
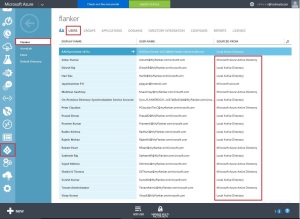
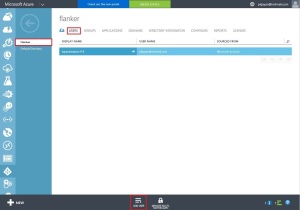
Now, enable the user account in your organization for MFA. Click on the USERS tab in the left top corner of the screen.
Click the check mark next to your user account you wanted to enable, then click the enable link on the far right hand side of the screen to enable MFA for this user.
When prompted for confirmation, click the enable multi-factor auth button.
Click Close on the Updates successful dialog when it appears.
The user account is now enabled for multi-factor authentication.
Next time the user signs in, he/she will be asked to provide and confirm the authentication information that will be used to perform MFA from that point onwards.
Register as a User for MFA
Once the MFA is enabled for the user, the user has to register himself for the multi-method of authentication verification.
When the user logs on to his application portal ( https://myapps.microsoft.com ) for the first time since the administrator has enabled MFA, After the user is authenticated the user is asked to provide additional security information: Your admin has required that you set up this account for additional security verification.
Click on the Set it up now button.
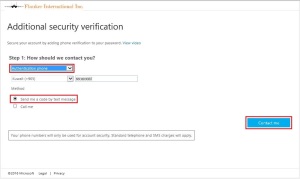
On the next page, you can choose among 3 contact methods:
- Authentication phone
- Office phone
- Mobile app
Select the Authentication phone contact method
Select the method Send me a code by text message
Select your Country and enter your Mobile number to receive the authentication code. Then click on Contact me
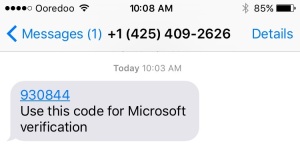
Enter the 6-digit code that you received on the next screen and click the Verify button.
In the additional security verification page, app password will be displayed. This password can be used instead of performing multi-factor authentication to access the application which is not MFA aware.
Click on Done to complete the MFA registration process.
You can always get back to it later by going to http://aka.ms/mfasetup.
You are done! The user will be prompted for MFA from now on whenever he/she sign in.
Once you click on Done to complete the MFA registration, the browser will refresh and bring back to the sign in page, Enter the 6-digit text message that is sent again to your phone.
Notice the checkbox Don’t ask again for 14 days, this option allows Azure to remember the device in the future so that it does not prompt you for MFA the next time your sign-in.
This is the same configuration option we enabled earlier with the Azure admin account.
Enabling additional MFA capabilities.
The above described MFA capabilities are included as part of the Office 365 license. we can utilize the Azure AD Premium license to leverage additional MFA capabilities such as Custom greetings, Fraud alert, Event Confirmation, Block/Unblock Users, Security Reports etc…
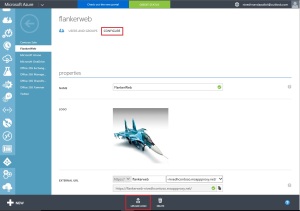
In order to configure these capabilities, click on ACTIVE DIRECTORY in the left navigation bar of the Azure administrative portal and select your directory where you have enabled Azure AD Premium licenses for users.
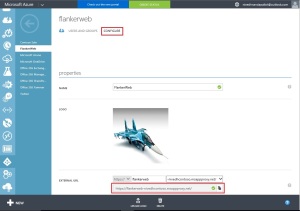
Click on USERS and then click on MANAGE MULTI-FACTOR AUTH at the bottom of the page.
Click on Service Settings and then click on Go to Portal at the bottom of the page
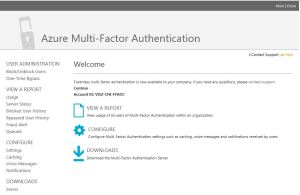
The following page will appear where you can configure advanced settings and also access Azure MFA reports.